Introduction
Two-Factor Authentication has become one of the most important tools for securing online accounts in an increasingly digital world. With cyber threats growing more sophisticated every day, relying on just a password is no longer enough. People reuse passwords, create weak ones, or unknowingly expose them through phishing attacks, making accounts vulnerable to hackers.
By adding an extra layer of security, this method significantly reduces the risk of unauthorized access. Whether you’re protecting personal data, financial information, or business systems, adopting stronger authentication practices is no longer optional—it’s essential.
What is Two-Factor Authentication?
Two-Factor Authentication (often called 2FA) is a security process that requires users to verify their identity using two different factors before gaining access to an account or system.
These factors typically fall into three categories:
- Something you know (like a password or PIN)
- Something you have (like a mobile phone or security token)
- Something you are (like a fingerprint or facial recognition)
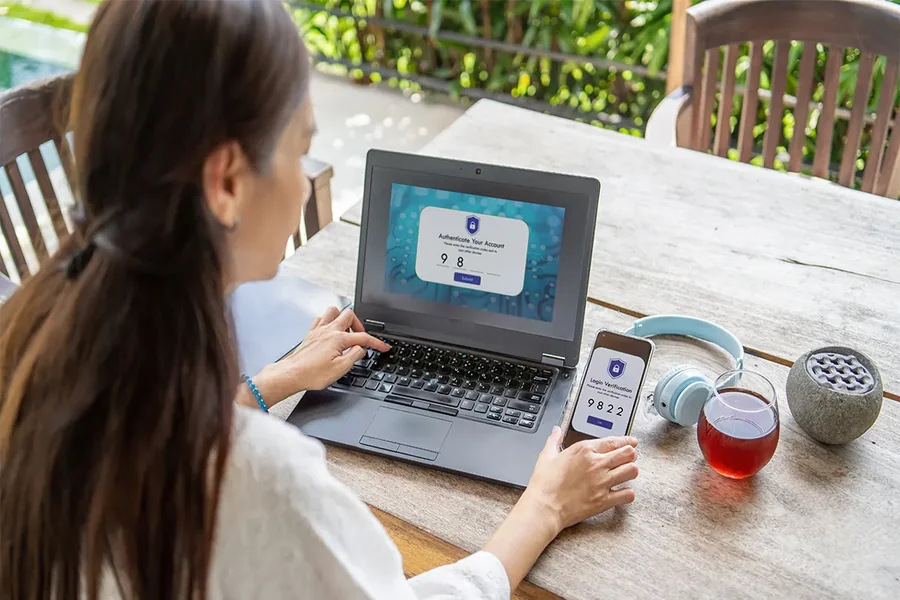
Instead of relying solely on a password, 2FA combines two of these elements. For example, after entering your password, you might receive a one-time code on your phone that you must enter to complete the login process.
This layered approach makes it much harder for attackers to break in, even if they manage to steal your password. For more information you can visit techpora.
Why Passwords Alone Are No Longer Enough
Passwords have long been the first line of defense, but they are also one of the weakest security measures today. Many users create simple passwords for convenience, reuse them across multiple platforms, or store them insecurely.
Cybercriminals exploit these habits using techniques such as:
- Phishing emails that trick users into revealing credentials
- Brute-force attacks that guess passwords automatically
- Data breaches that expose millions of login details
Once a password is compromised, an attacker can easily access accounts if no additional protection is in place. This is where multi-factor authentication becomes critical—it acts as a second barrier that stops unauthorized access even when passwords fail.
Key Benefits of Using Two-Factor Authentication
Implementing 2FA offers several significant advantages that go beyond basic security.
Stronger Account Protection
The most obvious benefit is enhanced security. Even if someone obtains your password, they still need the second factor—such as a verification code—to access your account. This dramatically reduces the chances of a successful breach.
Protection Against Phishing
Phishing attacks are one of the most common ways hackers steal credentials. With an extra verification step, stolen passwords alone are not enough, making these attacks far less effective.
Safeguarding Sensitive Data
Whether it’s personal emails, banking details, or company information, 2FA helps protect sensitive data from unauthorized access. This is especially important for businesses that handle customer information.
Increased User Confidence
When users know their accounts are protected by advanced security measures, they feel more confident using online services. This trust is essential for both individuals and organizations.
Compliance with Security Standards
Many industries now require stronger authentication methods to meet security regulations. Using 2FA helps organizations stay compliant and avoid potential penalties.
Common Types of Two-Factor Authentication
There are several ways to implement this security method, each with its own strengths and level of convenience.
SMS-Based Codes
One of the most widely used methods involves sending a one-time code via text message. While easy to use, it is not the most secure option due to risks like SIM swapping.
Authenticator Apps
Apps like Google Authenticator or Microsoft Authenticator generate time-based codes. These are more secure than SMS because they don’t rely on mobile networks.
Hardware Tokens
Physical devices generate secure codes or plug directly into a computer. These are highly secure but less convenient for everyday users.
Biometric Verification
This includes fingerprint scans, facial recognition, or voice identification. Biometrics provide a seamless and secure user experience but require compatible devices.
Challenges and Misconceptions
Despite its benefits, some people hesitate to adopt Two-Factor Authentication due to misunderstandings or perceived inconvenience.
One common concern is that it slows down the login process. While it does add an extra step, the few seconds required are a small price to pay for significantly improved security.
Another misconception is that 2FA is only necessary for high-value accounts like banking. In reality, any account—email, social media, or cloud storage—can be a target. Once compromised, these accounts can be used for identity theft, scams, or further attacks.
There is also a belief that strong passwords alone are enough. However, as cyber threats evolve, relying solely on passwords is no longer a reliable strategy.
Best Practices for Using Two-Factor Authentication
To get the most out of 2FA, it’s important to follow a few best practices.
First, enable it on all important accounts, including email, banking, and social media. Your email account, in particular, should be highly protected because it can be used to reset passwords for other services.
Second, choose more secure methods whenever possible. Authenticator apps or hardware tokens are generally safer than SMS-based verification.
Third, keep backup codes in a secure place. These can help you regain access if you lose your device.
Finally, avoid sharing verification codes with anyone. Legitimate services will never ask for these codes directly.
Final Thought
Two-Factor Authentication is no longer just an optional security feature—it is a necessity in today’s digital landscape. As cyber threats continue to grow in complexity, relying on passwords alone leaves users exposed to serious risks.
By adding an extra layer of protection, 2FA significantly reduces the chances of unauthorized access and helps safeguard personal and professional data. It is a simple yet powerful step that anyone can take to improve their online security.
In a world where data breaches and cyberattacks are becoming increasingly common, adopting stronger authentication methods is one of the smartest decisions you can make.